Подключим к hMailServer в качестве антивируса Windows Defender. Воспользуемся антивирусом, который уже имеется в ОС. У меня Windows Server 2016.
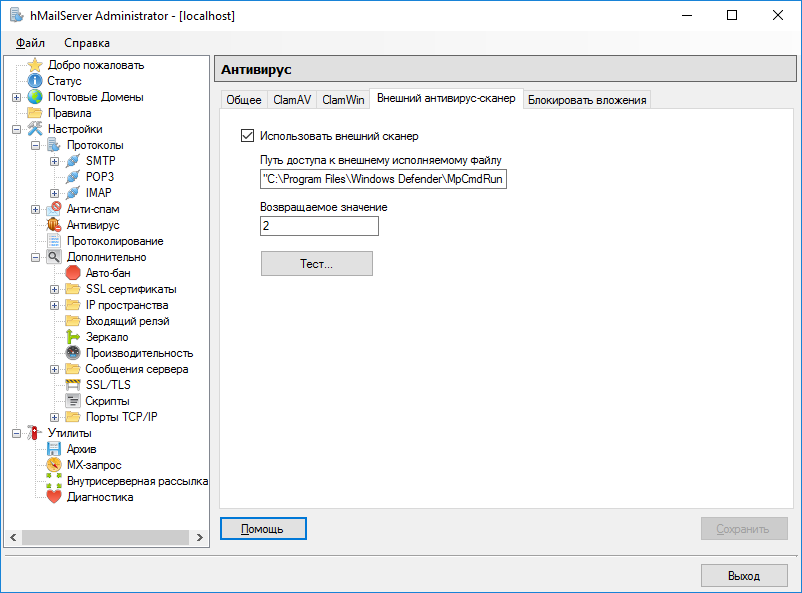
Открываем hMailServer Administrator, переходим в раздел Настройки → Антивирус. Вкладка Внешний антивирус-сканер.
Включаем галку "Использовать внешний сканер".
Путь доступа к внешнему исполняемому файлу:
"C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -Scantype 3 -File "%FILE%" -DisableRemediation
Возвращаемое значение:
2
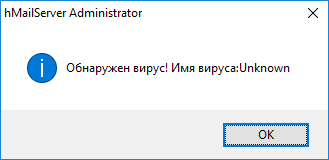
Нажимаем кнопку Тест...
Работает шарманка.
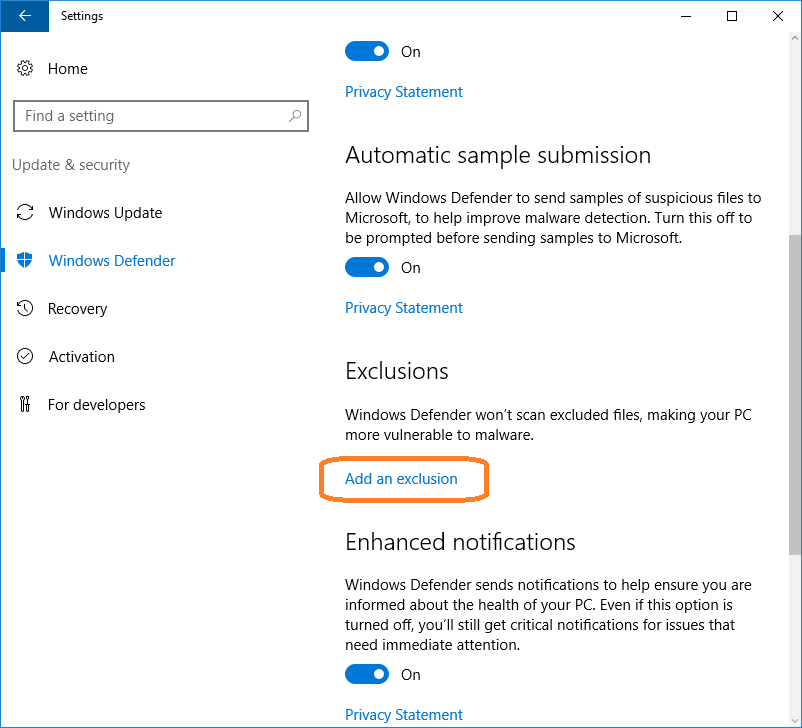
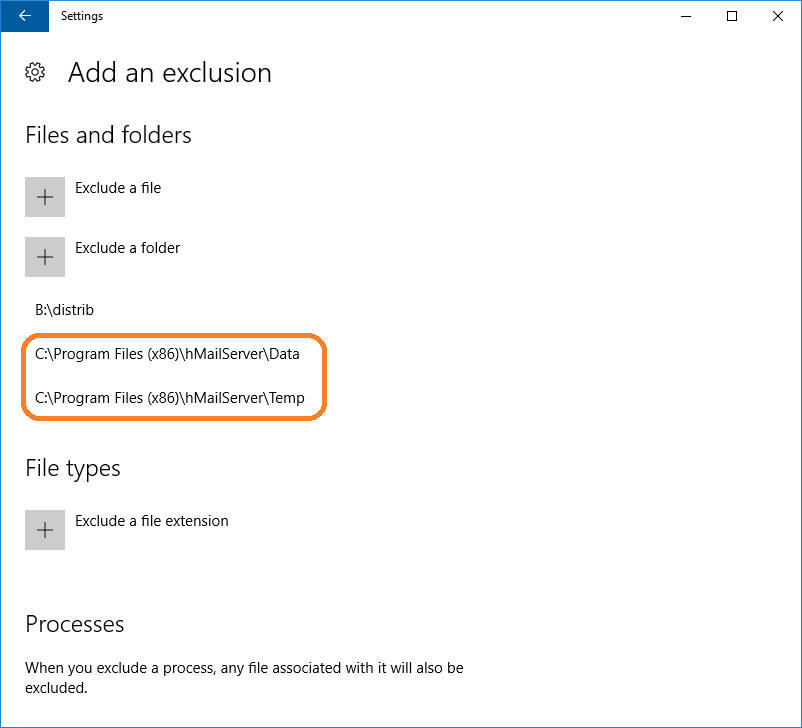
Теперь нужно настроить Windows Defender таким образом, чтобы активное сканирование не мешало проверке писем, для этого нужно внести пару исключений. Открываем настройки системы — Settings > Windows Defender.
Добавляем исключение — Add an exclusion.
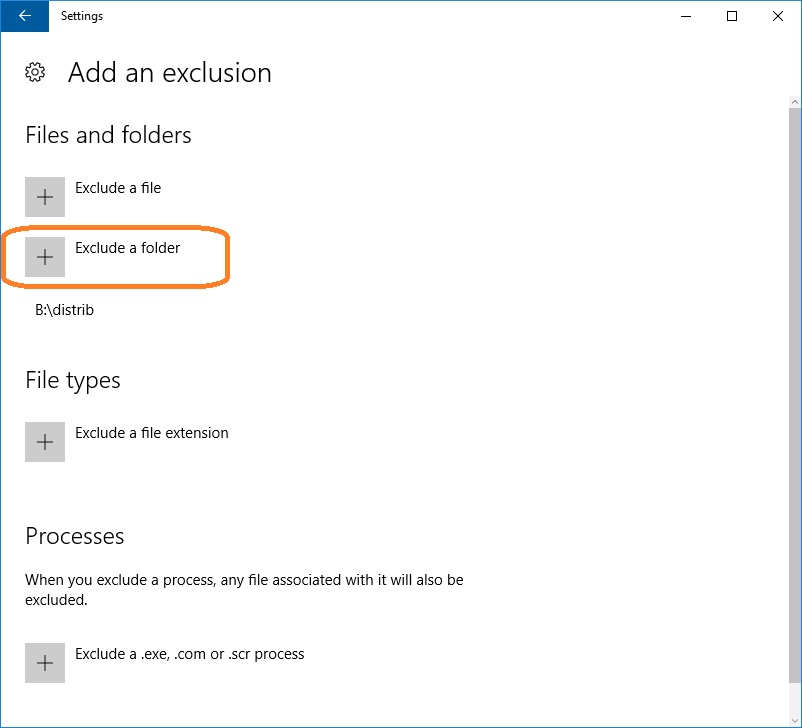
С помощью кнопки "Exclude a folder" добавляем в исключения две папки:
- C:\Program Files (x86)\hMailServer\Data
- C:\Program Files (x86)\hMailServer\Temp
Настройка завершена.
Дополнительно
Подробнее о параметрах MpCmdRun.exe можно узнать командой:
C:\Program Files\Windows Defender>MpCmdRun.exe -?
Microsoft Antimalware Service Command Line Utility (c) 2006-2015 Microsoft Corp
Use this tool to automate and troubleshoot Microsoft Antimalware Service
Usage:
MpCmdRun.exe [command] [-options]
Command Description
-? / -h Displays all available options
for this tool
-Scan [-ScanType #] [-File <path> [-DisableRemediation] [-BootSectorScan]]
[-Timeout <days>]
Scans for malicious software
-Trace [-Grouping #] [-Level #] Starts diagnostic tracing
-GetFiles Collects support information
-RemoveDefinitions [-All] Restores the installed
signature definitions
to a previous backup copy or to
the original default set of
signatures
[-DynamicSignatures] Removes only the dynamically
downloaded signatures
-SignatureUpdate [-UNC | -MMPC] Checks for new definition updates
-Restore [-ListAll | [-Name <name>] [-All] [-Path <path>]] Restore or list
quarantined item(s)
-AddDynamicSignature [-Path] Loads a dynamic signature
-ListAllDynamicSignatures List the loaded dynamic signatures
-RemoveDynamicSignature [-SignatureSetID] Removes a dynamic signature
Additional Information:
Support information will be in the following directory:
C:\ProgramData\Microsoft\Windows Defender\Support
-Scan [-ScanType value]
0 Default, according to your configuration
1 Quick scan
2 Full system scan
3 File and directory custom scan
[-File <path>]
Indicates the file or directory to be scanned, only valid for custom scan.
[-DisableRemediation]
This option is valid only for custom scan.
When specified:
- File exclusions are ignored.
- Archive files are scanned.
- Actions are not applied after detection.
- Event log entries are not written after detection.
- Detections from the custom scan are not displayed in the user interface.
- The console output will show the list of detections from the custom scan.
[-BootSectorScan]
Enables boot sector scanning; only valid for custom scan.
[-Timeout <days>]
Timeout in days; maximum value is 30.
If this parameter is not specified, default value is 7 days for full scan and 1 day for all other scans.
Return code is
0 if no malware is found or malware is successfully remediated and no additional user action is required
2 if malware is found and not remediated or additional user action is required to complete remediation or there is error in scanning. Please check History for more information.
-Trace [-Grouping value] [-Level value]
Begins tracing Microsoft Antimalware Service's actions.
You can specify the components for which tracing is enabled and
how much information is recorded.
If no component is specified, all the components will be logged.
If no level is specified, the Error, Warning and Informational levels
will be logged. The data will be stored in the support directory
as a file having the current timestamp in its name and bearing
the extension BIN.
[-Grouping]
0x1 Service
0x2 Malware Protection Engine
0x4 User Interface
0x8 Real-Time Protection
0x10 Scheduled actions
0x20 NIS/GAPA
[-Level]
0x1 Errors
0x2 Warnings
0x4 Informational messages
0x8 Function calls
0x10 Verbose
0x20 Performance
-GetFiles [-Scan]
Gathers the following log files and packages them together in a
compressed file in the support directory
- Any trace files from Microsoft Antimalware Service
- The Windows Update history log
- All Microsoft Antimalware Service events from the System event log
- All relevant Microsoft Antimalware Service registry locations
- The log file of this tool
- The log file of the signature update helper tool
[-Scan]
Scans for unusual files. The files and results of the scan
will be packaged in the compressed file.
-RemoveDefinitions
Restores the last set of signature definitions
[-All]
Removes any installed signature and engine files. Use this
option if you have difficulties trying to update signatures.
[-DynamicSignatures]
Removes all Dynamic Signatures.
-SignatureUpdate
Checks for new definition updates
[-UNC [-Path <path>]]
Performs update directly from UNC file share specified in <path>
If -Path is not specified, update will be performed directly from the
preconfigured UNC location
[-MMPC]
Performs update directly from Microsoft Malware Protection Center
-Restore
[-ListAll]
List all items that were quarantined
[-Name <name>]
Restores the most recently quarantined item based on threat name
One Threat can map to more than one file
[-All]
Restores all the quarantined items based on name
[-Path]
Specify the path where the quarantined items will be restored.
If not specified, the item will be restored to the original path.
-AddDynamicSignature -Path <path>
Adds a Dynamic Signature specified by <path>
-ListAllDynamicSignatures
Lists SignatureSet ID's of all Dynamic Signatures added to the client
via MAPS and MPCMDRUN -AddDynamicSignature
-RemoveDynamicSignature -SignatureSetID <SignatureSetID>
Removes a Dynamic Signature specified by <SignatureSetID>
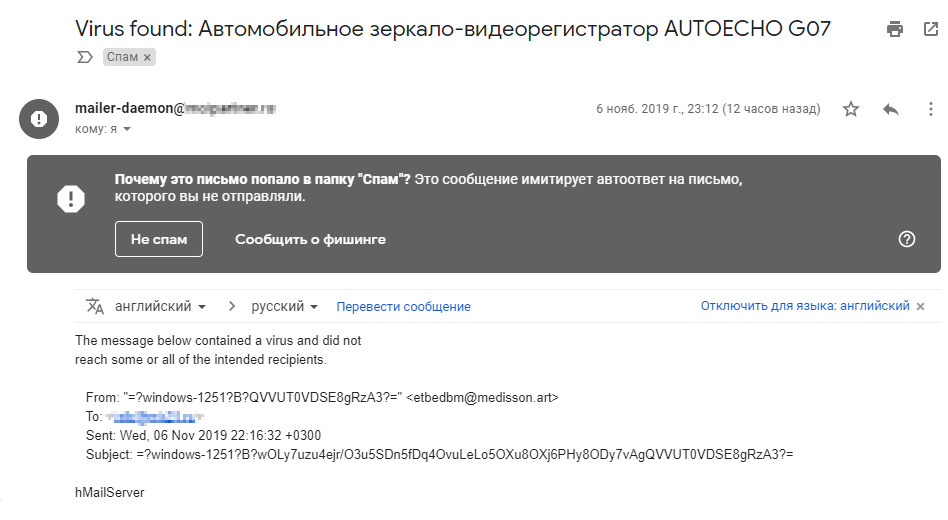
А вот и первый вирус...